Risk Management
In July 2010, the Risk Management Committee (RMC) was established. The Chairman and CEO serves as the Chairperson, while the President acts as the Vice Chairperson. The Chief Financial Officer concurrently serves as the Executive Secretary, and heads of all major departments are appointed as committee members. Management review meetings are held semiannually.
In 2020, the Board of Directors approved the establishment of the "Risk Management Policy and Procedures." In alignment with the "Guidelines for Risk Management Practices of TWSE/TPEx Listed Companies" issued by the Taiwan Stock Exchange on August 8, 2022 (Ref. No. 1110015360), the policy was revised and approved during the first Board meeting in 2023.
For details, please refer to the "Risk Management Policy and Procedures" available on the Company’s website.
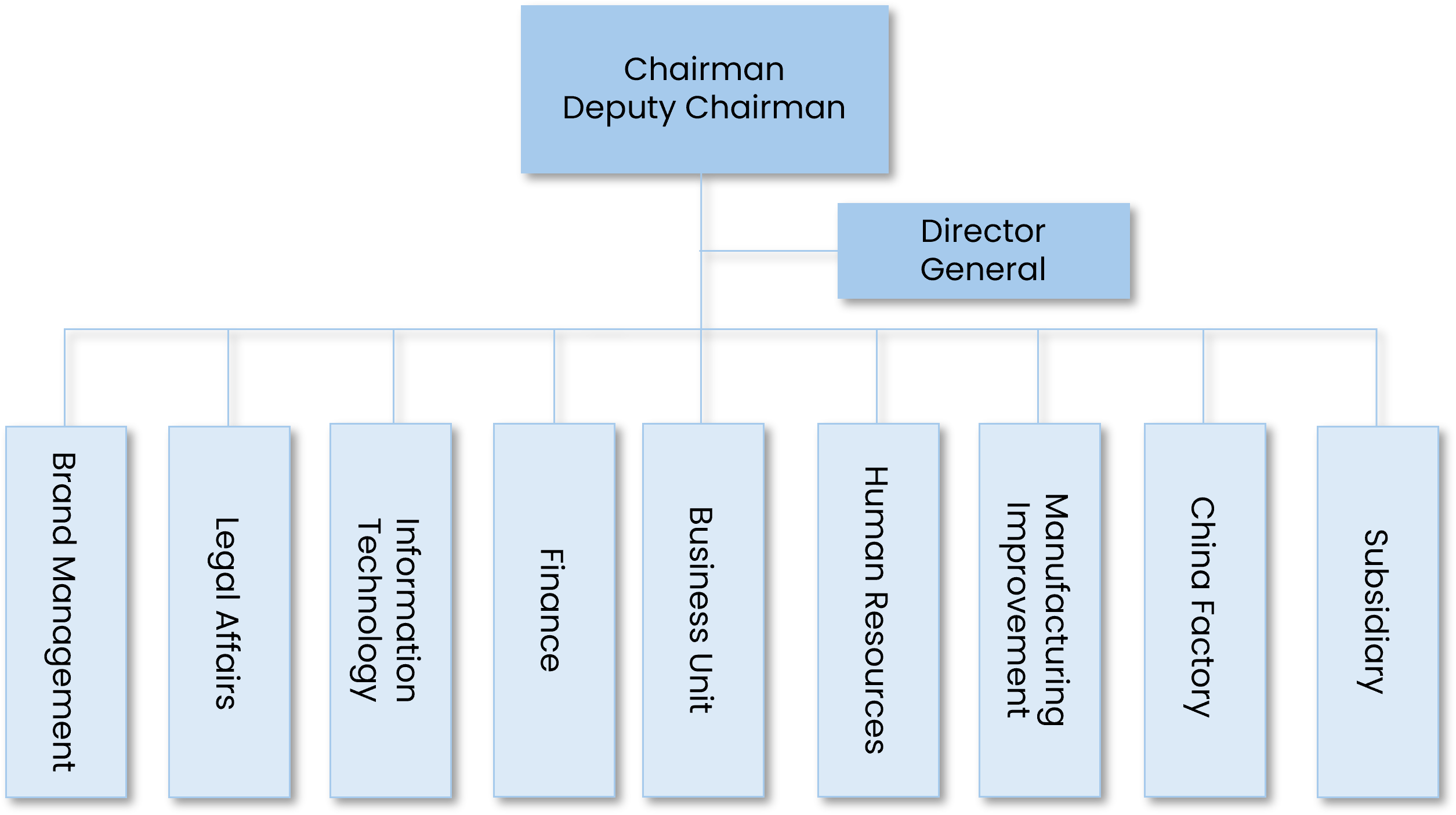
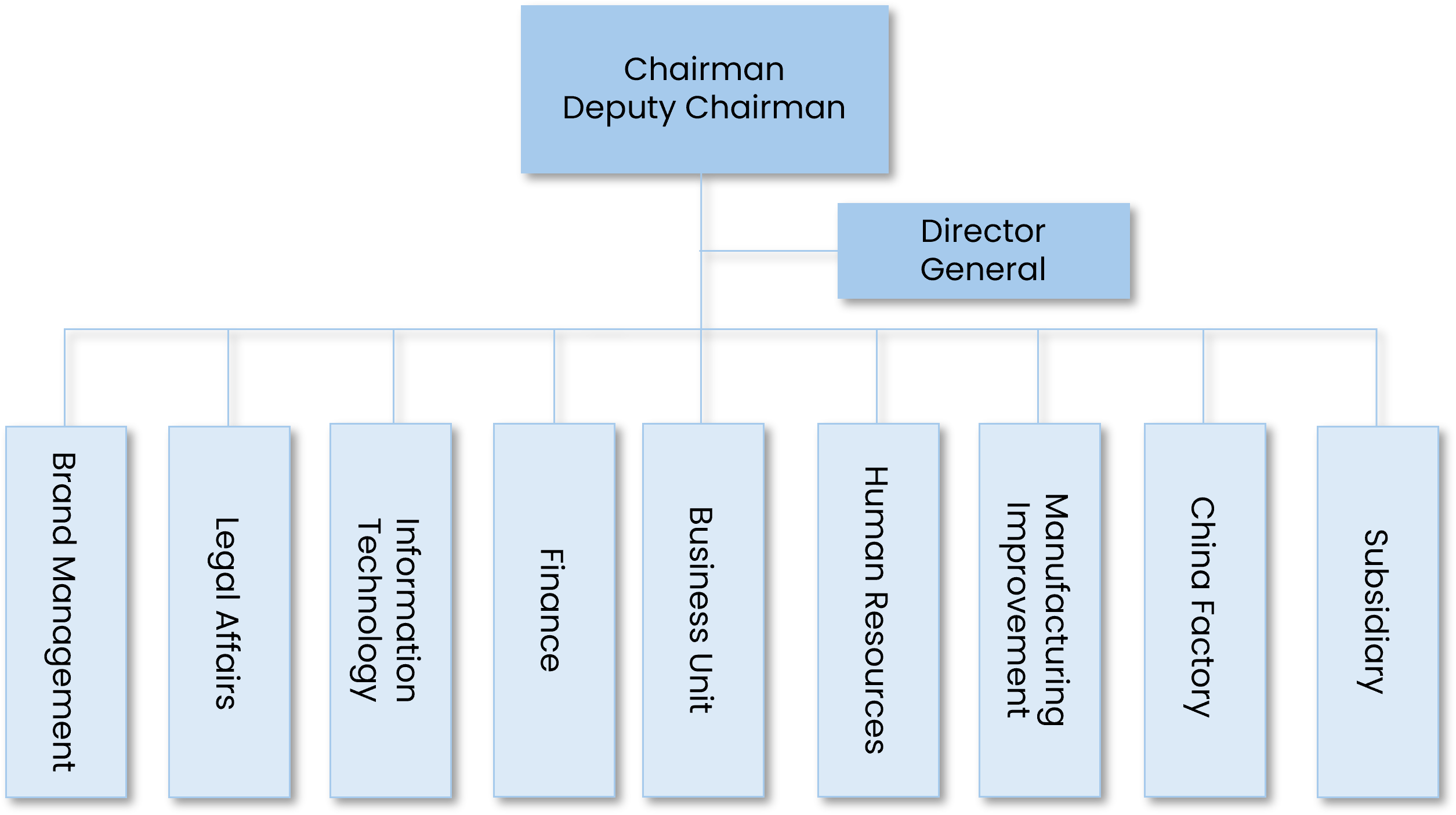
Risk Management Committee Organization
Risk Management Scope
The company’s risk management system, with a focus on corporate governance and risk transfer planning, is structured around four key dimensions: strategic risk, financial risk, operational risk, and hazard risk. Each dimension is further categorized into internal and external risks. Following the processes of risk identification, risk analysis, risk assessment, and risk monitoring, a risk radar management chart is generated.
In 2020, the Board of Directors approved the establishment of the "Risk Management Policy and Procedures." In alignment with the "Guidelines for Risk Management Practices of TWSE/TPEx Listed Companies" issued by the Taiwan Stock Exchange on August 8, 2022 (Ref. No. 1110015360), the policy was revised and approved during the first Board meeting in 2023.
For details, please refer to the "Risk Management Policy and Procedures" available on the Company’s website.
Risk Management Committee Organization
Risk Management Scope
The company’s risk management system, with a focus on corporate governance and risk transfer planning, is structured around four key dimensions: strategic risk, financial risk, operational risk, and hazard risk. Each dimension is further categorized into internal and external risks. Following the processes of risk identification, risk analysis, risk assessment, and risk monitoring, a risk radar management chart is generated.




